David Matousek recently published a threat model for OpenClaw that stopped me mid-scroll. Not because it was wrong — but because he was right, and we're already building the answer.
His three questions for assessing any AI agent architecture:
- What system privileges does the agent have?
- What can extend its capabilities?
- What governs its memory?
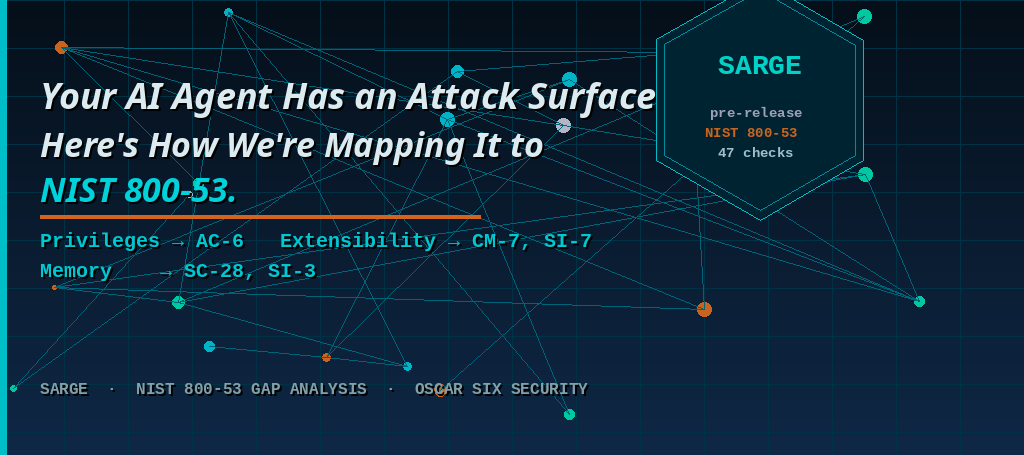
These aren't just good questions. They map directly to NIST 800-53 Rev 5 control families that enterprise security teams have been applying to traditional systems for years. The challenge is that nobody has done that mapping for AI agents specifically — until now.
His Framework, Translated to 800-53
Privileges → AC-6 (Least Privilege)
OpenClaw ships with shell access, browser control, email, and API access. No least-privilege defaults out of the box. AC-6 requires that users and processes operate with only the permissions necessary for their function.
For an AI agent, that means defining exactly what tools it needs — and hardening everything else. An agent that manages your calendar has no business touching your file system.
Extensibility → CM-7 (Least Functionality) + SI-7 (Software Integrity)
An open skill registry is a supply chain attack surface. CM-7 requires disabling unused capabilities. SI-7 requires verifying the integrity of software and tools.
For agent deployments, this means a vetted skill registry with checksum verification — not an open install-anything model. Cisco has already documented data exfiltration via third-party agent skills. This isn't theoretical.
Memory Governance → SC-28 (Protection at Rest) + SI-3 (Malicious Code Protection)
Context compaction that silently drops safety instructions is a real and documented risk. SC-28 covers protection of information at rest. SI-3 covers protection against malicious code — and prompt injection via memory content absolutely qualifies.
When your agent compacts its context window to save tokens and quietly discards the rule that says "never email external parties," you have a control failure. 800-53 has language for exactly this scenario.
What We're Building
Sarge is an open source NIST 800-53 gap analysis tool built specifically for OpenClaw deployments — currently in pre-release development. It runs 47 checks across 6 control families — including AC-6, CM-7, SI-7, SC-28, and SI-3 — and tells you exactly where your deployment stands.
It produces a structured report: control ID, pass/warn/fail status, current value, required value, and remediation steps. Hardening scripts are included. Everything runs locally — nothing leaves your machine.
David's post asks the right questions. Sarge is being built to give you the answers.
Why This Matters Beyond OpenClaw
The three-question framework David outlined works for any agent architecture — not just OpenClaw. As AI agents move from demos to production deployments, security teams need a structured way to assess them. NIST 800-53 is that structure. It predates AI agents by decades, but the controls map with surprising precision.
The industry is going to need this. We're building it now.
→ Read David's original post and threat model diagram
→ Sarge on GitHub — pre-release
Star the repo to follow progress. Pre-release contributors welcome.